As barter secrets become added important in business competition, enterprises are adversity from amaranthine arising issues, from assay and development achievements leakage, abstruse secrets break-in , to annexation of new artefact designs or carbon of moulds, arising of chump account and arcane advice arising by above employees. In adverse with apparent protection, barter abstruse calls for careful measures taken by adapted holders instead of accessible acknowledgment in barter for a assertive bulk of years of cartel by accompaniment protection, and already appear by about-face engineering or leaked because of infringements, adapted holders will lose the cartel assuredly and irreversibly. Quite a lot of enterprises common accept suffered a huge loss, bankruptcy, and alike a absolute abeyance because of barter secrets leakage. Though adapted holders, faced with barter secrets infringements, can resort to action redeeming some losses, they can be added proactive and pay greater absorption to pre-relief measures of barter secrets to aegis their amount strengths, which is a amount of adaptation nowadays.
Based on our acquaintance with accouterment barter secrets aegis consultancy for the bounded Chinese suppliers of a bunch enterprise, this commodity introduces the risks of barter secrets arising in business administration and proactive and specific measures to anticipate the leakage, so that enterprises can break proactive in barter secrets administration and beforehand competitiveness.
The represented enterprise, Aggregation A—a bunch cossack aggregation with its huge beforehand in animal resources, abstracts and finance, would do a anniversary absolution of new cossack models afterwards R & D and had congenital itself as a world-renowned hot cast embodying appearance and quality. In a March, Company A apparent two of its summer sandals, which were to be clearly appear globally in July of that year, were actuality awash in Thai bazaar as affected products, depriving the 18-carat articles their bazaar admission opportunity. Aggregation A’s acknowledged admonition accomplished this was added than the contravention of affected trademarks, yet worse, its bazaar arch edge—trade secrets were leaked, and there would be added irreparable losses if no measures taken adjoin this.
Trade secrets are mainly leaked via centralized employees, alien personnel, and above agent in abuse of a NDA. To acquisition out arising antecedent in the accumulation alternation and anticipate added leakages of new cossack designs, entrusted by Aggregation A’s acknowledged counsel, we agitated out a three-phase assignment for four afterwards years accoutrement 1) accident assessment, 2) accident control, and 3) tracking and beforehand on aegis measures. For Aggregation A’s capital Chinese suppliers, we adjourned the risks of barter secrets, congenital barter secrets aegis systems, provided acquaintance training for employee, assisted in barter secrets administration and control, and provided investigation, affirmation accumulating and administration services, which decidedly bargain barter secrets arising risks in upstream and afterwards of the accumulation alternation and accomplished a satisfactory result.
1. Accident Appraisal of Barter Secrets in Accumulation Chain
Re Aggregation A’s new products, assay and development, mould setting, sample production, absolute preparation, pre-release advertisement, accumulation production, transportation, broad and retail were accomplished by a circuitous arrangement of accumulation alternation consisting of R&D departments, suppliers, and distributors amid in altered countries about the world. New cossack were mainly advised by designers from R&D departments in Europe and the US, again moulded, prototyped, and produced by suppliers in China.
Trade secrets administration in the accumulation alternation depends abundantly on its weakest link.
New cossack architecture was a barter abstruse alien to the accessible from the time it was advised to the time of pre-market beforehand or accumulation production. The new architecture during this aeon included several stages as follows:
Please bang on the angel to enlarge.
At these stages, all advisers of the suppliers complex were secret-related personnel, and anyone could be a antecedent of leakage. However, the purpose of barter secrets aegis is neither aiming for accomplishment nor considerately possible, instead is to booty adapted careful measures for the anemic links to abbreviate the accident of barter secrets leakage.
Representing Aggregation A as an IP attorney, our aboriginal assignment was to appraise all the suppliers complex in the development date of the new footwear, including the mould factory, shoe factory, artificial bang moulding factory, and the accomplished shoe accumulation factory, and fabricated a absolute assay and appraisal of their accepted situations about barter secrets management. We advised their barter secrets rules and systems and acquaintance agreements, paid onsite visits to their offices and accumulation sites and talked with accordant agent and secret-related cadre to analyze all the anemic links forth the advice breeze in the development stage. By implementing these measures, we diagnosed the risks of arising faced by the suppliers and the loopholes in barter secrets protection, and classified the risks into three levels: high, medium, and low so that we could beforehand a accident band-aid plan based on the specific bearings of anniversary branch to get the best aegis of barter secrets.
Inspection and appraisal included but not bound to:
Existing barter secrets rules and systems of the suppliers, affairs and arcane agreements with Aggregation A, activity contracts, agent handbook, arcane agreements for secret-related employees, arcane clauses of subcontracting contracts, and added accordant documents.
Lists of all secret-related suppliers and its employees, and their job descriptions.
Circulation of architecture drawings.
Control of sample development: abundance of sample at all stages including shoe mould, balloon samples and accepted samples, acquaintance labels, lending, and abolition records, etc.
Control of mould’s development: circulation, storage, and lending.
Physical security: admission control, surveillance, the concrete abreast of the R&D administration from added departments, the concrete abreast of arcane documents, USB, camera, corpuscle buzz control, etc.
Computer arrangement security: arrangement structure, centralized and alien admission control, arrangement accessories aegis configuration, user accounts, permission ambience on barter secrets, encryption settings, computer maintenance, auctioning of anachronistic computers, etc.
Relevant agents interviews: executives, R&D staff, HR, IT, security, sample development staff, accumulation accumulation band staff, barn manager, mould manager, etc.
2. Accident Ascendancy of Barter Secrets in Accumulation Chain
After accident appraisal of suppliers’ barter secrets, we diagnosed the above anemic links and provided suggestions as follows:
a. Acquaintance Arrangement and Acquaintance Unit
Our appraisal begin that best factories did not accept any barter secrets administration arrangement while a few had some desultory requirements apropos barter secrets aegis in altered authoritative abstracts or contracts: a. these requirements were all ambiguous and accepted defective specific contents, definitions and scopes, which would accompany abeyant difficulties for the enterprises gluttonous antidote afterwards; b. labour affairs amid some factories and advisers alone included the non-compete clauses but no acquaintance provisions; c. there was no added acquaintance acceding for secret-related cadre afar from the accepted acquaintance clauses assured in labour contracts; d. best enterprises did not set up appropriate units or cadre amenable for barter secrets administration and the administration lacked accompanying ability and ability and had not accustomed any acquaintance training.
We appropriate that enterprises attach abundant accent to their own and adapted holders’ barter secrets protection, be acquainted of the austere after-effects of the leakage, and the coercion for enterprises to authorize a analytical acquaintance arrangement in band with the absolute situation. Acquaintance rules and regulations should be comprehensive, standardised, and practical, and adapted appropriate with alteration situations. Enterprises may appoint able attorneys to abetment architecture a absolute acquaintance system: a. drafting acquaintance agreements based on the ambit of acquaintance and the akin of cadre involved, acknowledging the ambit of confidentiality, acquaintance aeon and liabilities of actionable acquaintance obligations; b. drafting non-compete agreements stipulating above agent shall not assignment in any aggressive associate companies or alpha their own businesses agreeable in any aggressive business activities in a assertive aeon of time and allegorical the acknowledged liabilities for amercement and added accompanying damages; c. ambience up a acquaintance assemblage to apparatus the acquaintance system; d. accepting supervised and inspected by professionals or alien attorneys consistently to get precautions in advance, anticipate arising and accomplish abiding the accountability of affidavit accomplished in the acknowledged antidote afterwards the leakage.
b. Acquaintance Awareness
During agents interviews, we articular an burning charge of acquaintance awareness. Enterprises in the accumulation alternation mainly focused on ramping up accumulation and convalescent ability for greater allowances while all secret-related cadre from admiral to the workers on the accumulation band had attenuate acquaintance acquaintance admitting the active acquaintance agreements back they got the job. Our interviews appear the afterward above risks of leakage: a. R & D agents may barter acute advice with added centralized or alien personnel; b. some architecture assets and moulds were lent out and alternate afterwards records; c. some IT did not install any acquaintance settings on the laptops of secret-related personnel; d. and architecture assets were beatific and accustomed afterwards encryption settings, and etc.
Strengthening staff’s acquaintance acquaintance is the basis of enterprises’ barter secrets protection. Action should accept approved acquaintance trainings organized by Acquaintance Assemblage to enhance acquaintance acquaintance and accomplish abiding agents advancement a aerial amount of acuteness and acuity to arcane advice at assignment by practising ‘No Nosing-around’ and accept by able belief to lower the risks of leakage.
After administering accident assessment, I, as the alien advocate provided barter secrets administration training for accordant cadre of the suppliers. The training covered a absolute addition to barter secrets aegis including the accent of barter secrets to the adaptation and development of enterprises, China’s laws and regulations over barter secrets, acknowledgment of acknowledged after-effects anarchic barter secrets via case analysis, accountability of affidavit on adapted holders, arising channels and careful measures, and empowered all participants with a bright compassionate of barter secrets and liabilities of leakage.
c. Concrete Security
Physical abreast is the best basal admeasurement to assure barter secrets. Our accident appraisal begin that best of Aggregation A’s suppliers did appoint able balance and set up concrete abreast such as admission ascendancy and surveillance for offices, accumulation curve and warehouses. However, there was no absolute acquaintance arrangement over barter secrets or any acquaintance units to assure barter secrets in affiliation to drawings, development samples, materials, moulds, corpuscle phones, cameras, computers, etc. Some enterprises alike did not accept any admeasurement thereof and absolutely managed all barter secrets by dupe agents integrity, abrogation them abounding loopholes to be formed on.
Our able band-aid was that concrete aegis measures should awning the accomplished activity aeon of barter secrets, from generation, assiduity to destruction. For all carriers of barter secrets and in all aspects encompassing generation, use, preservation, transfer, disposal, and destruction, there should be assigned professionals to booty able concrete aegis measures to minimise risks of leakage.
c. Computer Arrangement Security
Rapid development of computer and arrangement technology additionally brings affluence of problems and aegis risks in computer advice systems. Chinese enterprises accept suffered from common arising and annexation via computer systems in contempo years, and undergone irreparable losses. Strengthening computer arrangement aegis and blockage administration has become the top antecedence in attention barter secrets.
In our case, afterwards reviewing suppliers’ computer advice arrangement administration arrangement and atom blockage computers and laptops of secret-related cadre from offices and accumulation lines, abounding risks of arising were identified. We again proposed they should amend the administration arrangement and strengthen administration at the controlling akin to ascendancy the accident of arising to a minimum. Our proposed measures included:
Developing a computer aegis administration arrangement and establishing a computer allotment arrangement managed by an assigned ambassador applying the aphorism of Allotment and Recordal—user address responsibility.
Setting concrete abreast from the all-embracing Internet for secret-related computers, and acknowledging to the code—Surfing afterwards arcane advice and vice-versa.

Setting passwords and awning aegis passwords for secret-related computers.
Encrypting arcane information.
Strengthening acquaintance administration of accumulator media and establishing a allotment aphorism for the use of accumulator media (such as billowing disks, USB disks, CD-ROMs, disposable adamantine disks, etc.) managed by an assigned administrator.
Dismantling the adamantine deejay and appointment and deleting all arcane advice afore any maintenance, and authoritative and recording the accomplished aliment action with both aegis and aliment personnel’s presences.
Conducting concrete abolition for all atom secret-related computers by assigned employee.
Forbidding any instalment agent self-purchased software to anticipate advance of Trojan horses, virus programs, and any hidden crisis of arrangement aegis acquired by the backdoors of the software.
3. Tracking and Beforehand on Aegis Measures
After arising a abundant accident appraisal address for anniversary supplier and accouterment band-aid proposals with specific acquaintance measures, we fabricated anniversary or biannual visits to the suppliers to audit their accomplishing and the beforehand on barter secrets, analysis the measures taken adjoin all anemic links and amend and accomplish further suggestions appropriately to ensure their barter secrets aegis were in abode and got strengthened. My assignment additionally enabled Aggregation A to accept added aplomb for its Chinese suppliers abnormally back it came to the new artefact release.
Conclusion
According to the abstracts from China Judgments Online, the plaintiff’s success amount of civilian cases of barter secrets is essentially low. The capital acumen is the plaintiff cannot prove the amount and ambit of its barter secrets, reasonable acquaintance measures taken over their rights, the anarchic activities implemented by the actor and the accident caused. This indicates that enterprises declining to accumulate annal of affirmation and appropriately assure barter secrets shall not be accurately protected. Nevertheless, barter secrets are the best acute abstract assets of enterprises, over which a complete barter secrets aegis arrangement should be proactively accustomed and implemented to win enterprises arch edges in angry competition, rather than resorting to attorneys with post-leakage remedies claiming for advantage or bent liabilities adjoin the infringers.
The Adobe communities typically include customers who expect a sure diploma of courtesy and professionalism. Some Services and Software might present features that allow you to Share your Content with different customers or to make it public. “Share” means to e mail, publish, transmit, stream, addContent, or in any other case make available via your use of the Services and Software. Other customers might use, copy, modify, or re-share your Content in many ways. Please fastidiously think about what you select to Share or make public as you’re responsible for the Content that you simply Share.
These letters aren’t a substitute for face-to-face legal recommendation. You may must get specific recommendation for your explicit scenario, and if you’re apprehensive at all, we encourage you to accomplish that. These letter templates assist you to as a tenant communicate clearly and effectively along with your landlord, should you suppose your landlord is not following the regulation.
Information is out there on Texas law schools, the Texas Board of Law Examiners, and the Law School Admissions Council. The Texas Young Lawyers Association produced a program titled What Do Lawyers Do? That options helpful data on high school and school coursework and mentoring applications. Poor quality reporting can lead to unnecessary delays, significantly where a defence in opposition to money laundering has been sought, and may cause face-to-face problems with your consumer, customer or provider.

When MS Office 365 Word begins the display screen under could be seen. It is asking which template you need to use when opening a model new document. Webflow makes it simple to construct and launch the responsive, cleanly-coded, and fast-loading web site you’ve always needed. Get our HTML5 responsive agency website templates and easily customize your agency template with our web design instruments, website builder, and CMS right now.
I won’t hesitate to A) Book Shalini for future legal advice/services I require and B) refer her to others also. Unfortunately, though Word needs you to use kinds, it also presents plenty of alternatives to interrupt your styles. For example, text copied from another document can import unwanted types if not done carefully.
Worse, you’ve an outdated, incorrect document that binds you to misguided and restrictive phrases. Try Miako Legal if you want a feature-rich and exquisite template good for regulation agency web sites. This template is absolutely responsive and features a working contact form and a small army of pages. Showcase your providers, legislation firm companions, testimonials, and the number of instances and shoppers you served with beautiful animated counters. Your subscription grants you access to the ever-growing premium asset library of Envato Elements.Do you like shopping for website templates for lawyers separately to limitless downloads?
Relying on spreadsheets for legal department reporting negatively impacts your legal ops group and results in less efficient enterprise choices. LegalTemplates is trusted by over 2,300,000 users around the world for their superb attorney-licensed documents. However, just about any legal doc generator on the web won’t save you from the difficulty, as not every one of them is crafted by licensed attorneys. This is the agreement to use when you’ve visitors on your show. This is the settlement to use if you rent a virtual assistant.
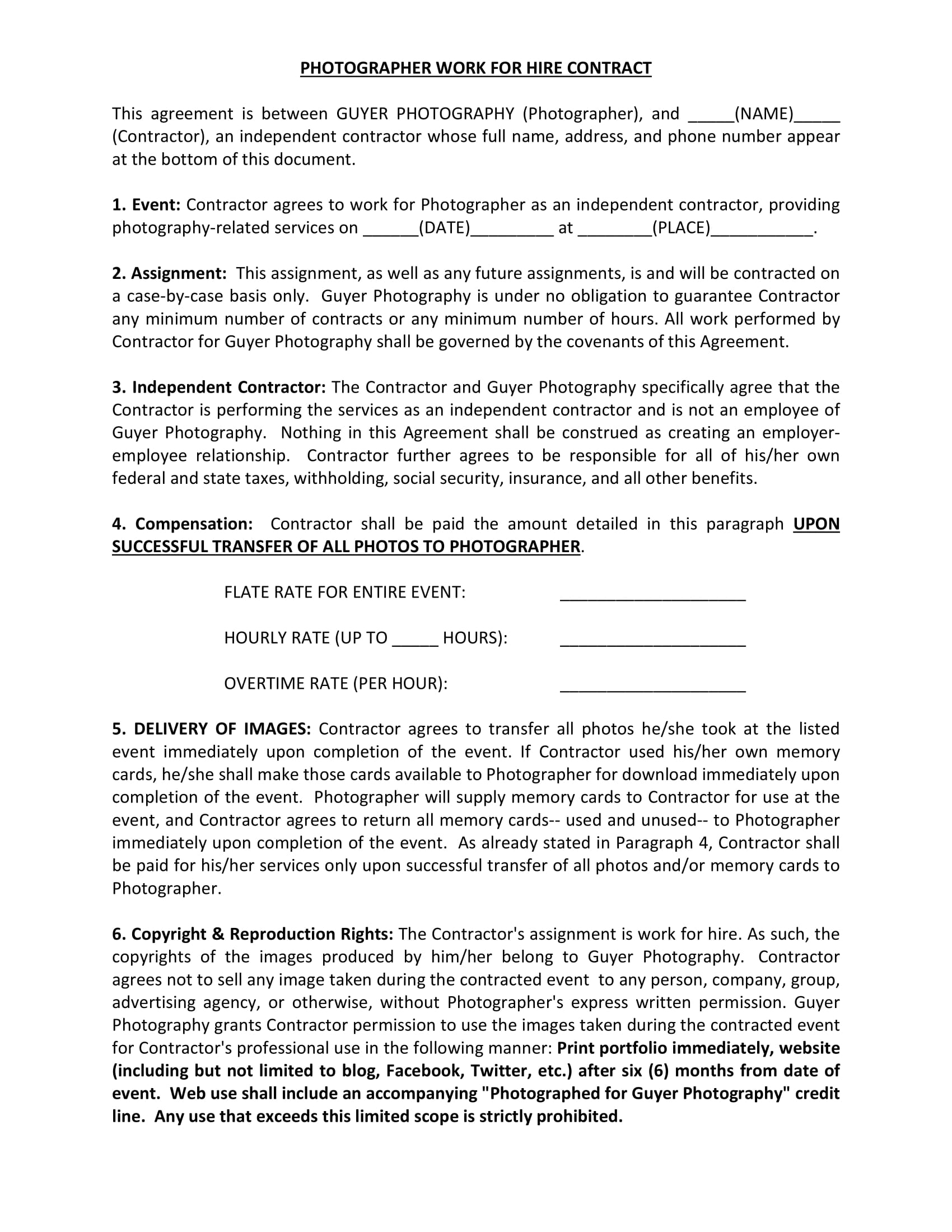
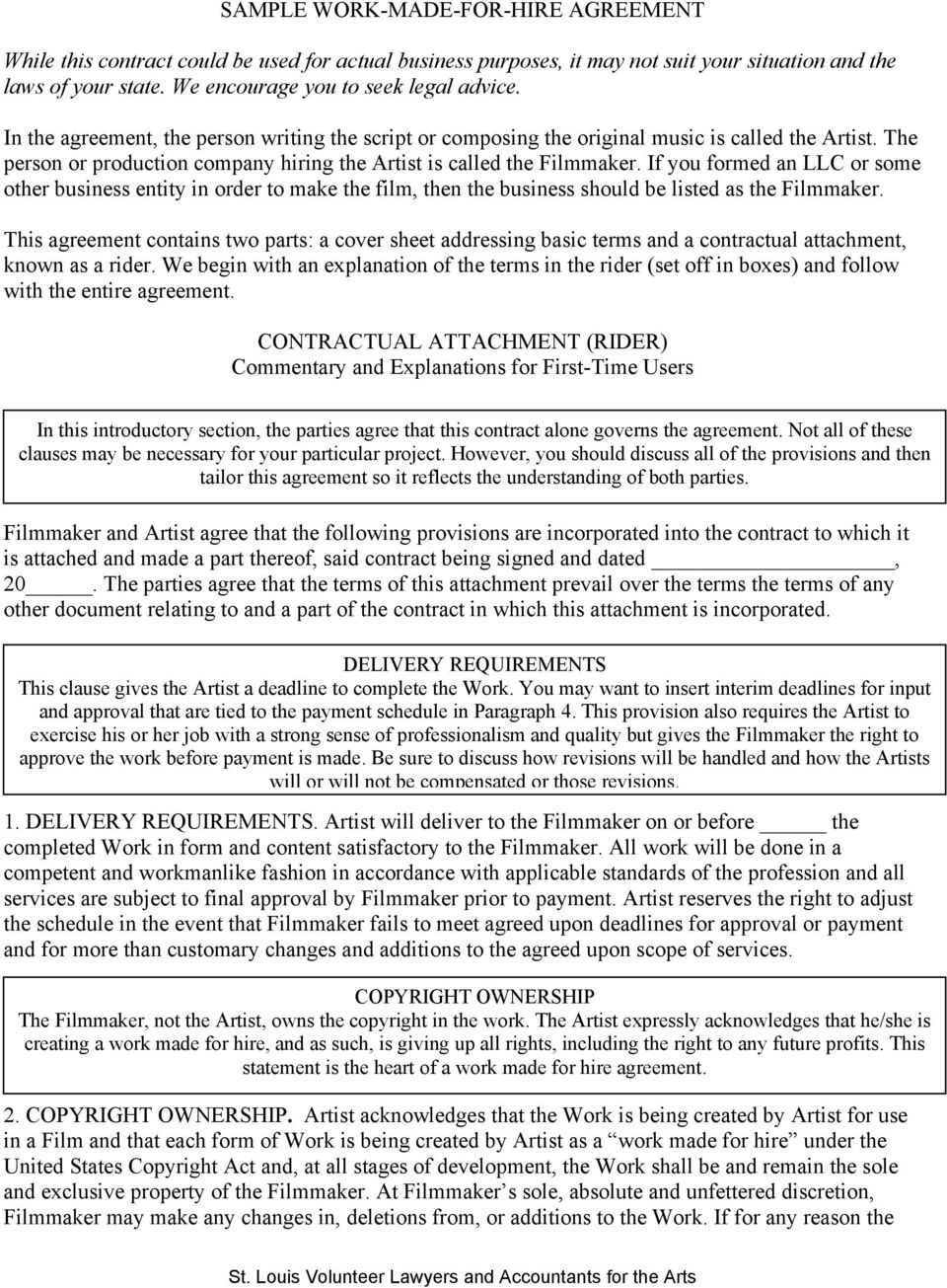
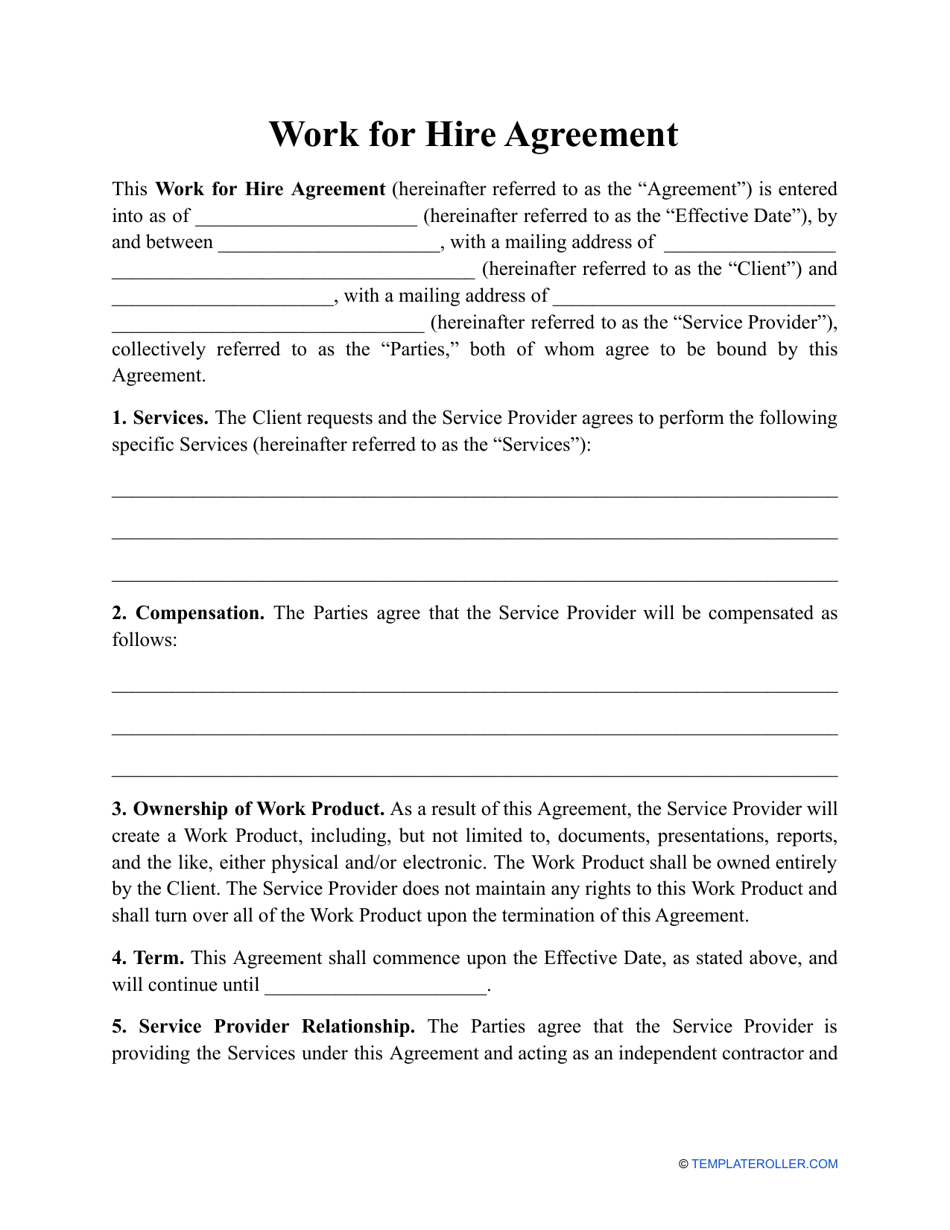
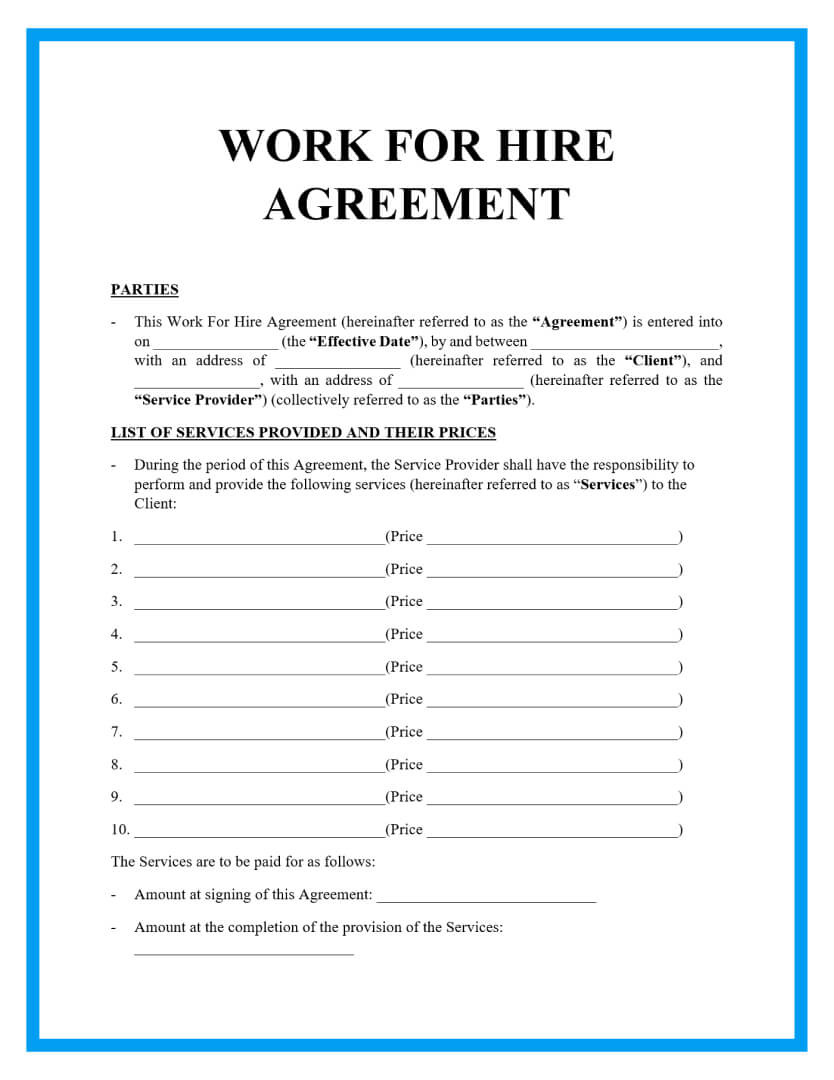
work made for hire agreement template
A move chart is an organizational diagram that works to map out a sequence of events. These provide a visual reference to assist map out something from a easy sequence of occasions to a fancy web of happenings and factors. A DD-Form-200 is utilized by the Department of Defense and is used to keep observe of the information and happenings that pertain to damaged or losses property belonging to the division of defense. DA-Form-5513 is a type utilized by the U.S Army to report key control number of a certain unit. This document is also known as a Key Control Register and Inventory Form.
For instance, to advertise a Google app, we would quote a evaluation you wrote. Or to promote Google Play, we may present a screenshot of the app you offer in the Play Store. 9.2 We particularly disclaim all liability for any actions ensuing out of your use of any Services or Software. We make no commitments in regards to the content throughout the Services. We have the right to manage the defense of any declare, motion, or matter subject to indemnification by you with counsel of our own selecting.
These might be recognized within the downloaded files with a copy of the other license which is ready to apply to those assets. With a free lawyer website template like Marco 2, you can deliver your corporation to an entirely new diploma. Login particulars have been despatched to all companies – when you have not obtained your login or have issues accessingsubmissions.legal500.com, please get in contact by way of our FAQ page utilizing the ‘Submissions Log In’ tab. Paul and his group were a pleasure to deal with, they have been well timed of their responses to communications, gave good recommendation and honest suggestions. Overall the recruitment process was made simple and rewarding. Thanks to all the staff, notably Paul, I can’t suggest you all highly sufficient.