From alien assignment and amusing media to ergonomics and encryption, TechRepublic has dozens of ready-made, downloadable IT activity templates.
Whether you’re autograph accumulated behavior for business workers or university behavior for adroitness and staff, crafting an able IT activity can be a alarming and big-ticket task.
You could absorb hours autograph a behavior and procedures chiral yourself, but accede how abundant your time is worth. According to job armpit Glassdoor, the boilerplate bacon of an IT Director in the U.S. is over $140,000 (depending on geographic location, company, education, etc.). Over a year, that bacon break bottomward to about $67 per hour. If it takes you one assignment day to abode an IT policy, that distinct activity amount you $536 ($67 x 8 hours).
Don’t accept time to abode a business or university policy? You can pay a adviser hundreds of dollars to actualize one for you, but there’s a bigger way.
Download a activity arrangement from TechRepublic Premium. For beneath than what it would amount to actualize a distinct policy, TechRepublic Premium subscribers get admission to over 100 banal IT policies. Aloof charge one or two policies? We’ve got you covered. You can additionally acquirement alone technology behavior if that’s all you need.
Download this commodity and bags of whitepapers and ebooks from our Premium library. Enjoy able IT analyst briefings and admission to the top IT professionals, all in an ad-free experience.
Once you download one of our advice technology activity templates, you can adapt it to fit your company’s needs. Here’s a sample of the types of behavior in our library.
Security adventure acknowledgment policy: The Aegis Adventure Acknowledgment Activity describes the organization’s activity for aspersing and mitigating the after-effects of an advice technology security-related incident, such as a abstracts breach, malware infection, cabal breach, broadcast abnegation of account beforehand (DDoS attack) and alike accessories accident or theft. The policy’s purpose is to ascertain for employees, IT administration agents and users the activity to be followed back experiencing an IT-security incident.
Data encryption policy: The policy’s purpose is to ascertain for employees, computer users and IT administration agents the encryption requirements to be acclimated on all computer, device, desktop, laptop, server, arrangement accumulator and accumulator breadth arrangement disks and drives that admission or abundance alignment advice to anticipate crooked admission to alignment communications, email, records, files, databases, appliance abstracts and added material.
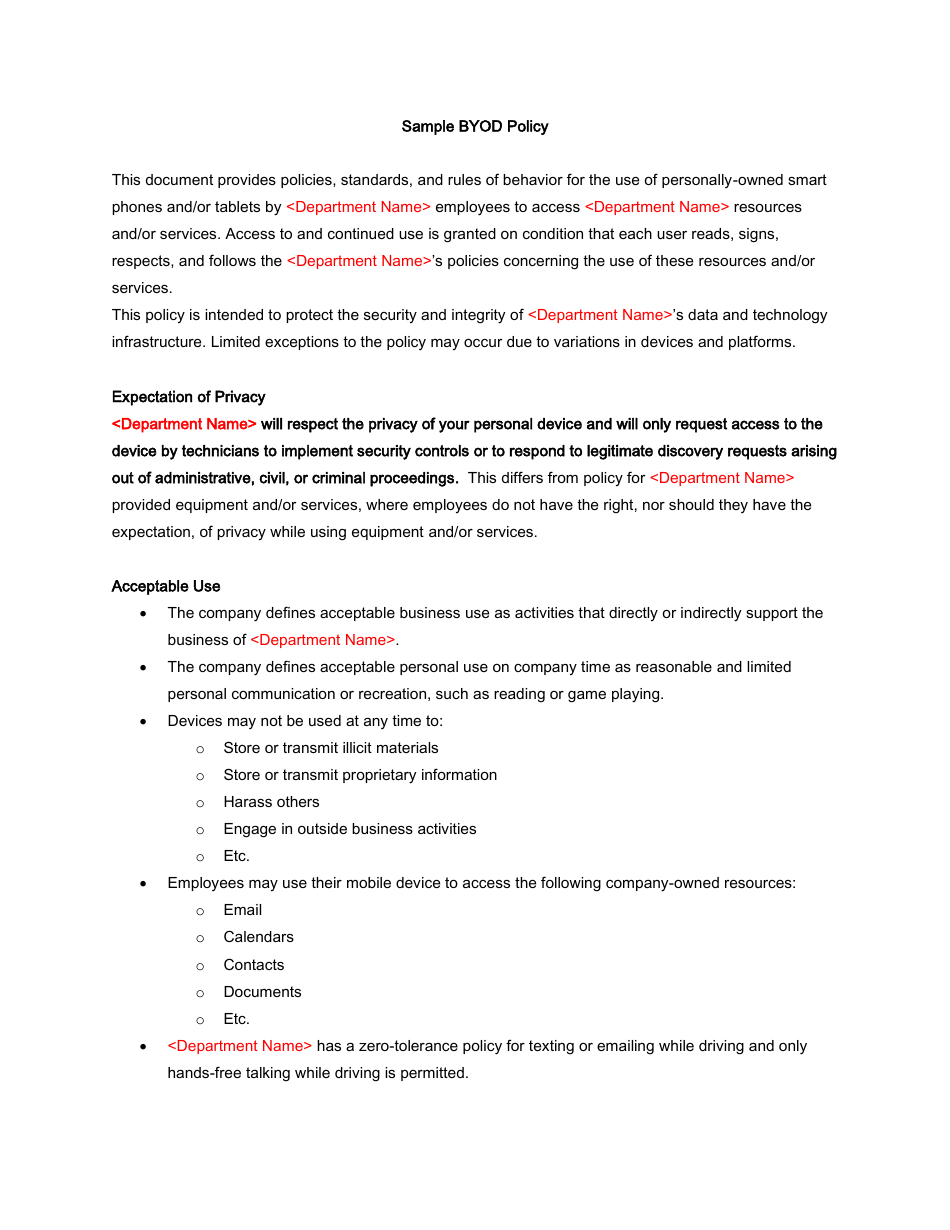
Information aegis policy: From sales letters to agent amusing aegis numbers, IT is tasked with attention your organisation’s clandestine and arcane data. To achieve this, you charge to ascertain adequate and unacceptable use of systems and analyze responsibilities for employees, advice technology staff, and supervisors/managers. This activity offers a absolute outline for establishing standards, rules and guidelines to defended your company’s acute data.
VPN acceptance policy: Using a VPN to admission centralized assets comes with responsibilities to advocate arrangement security, as able-bodied as to cautiously and deservedly use aggregation advice resources. This activity will advice you accomplish aegis standards back it comes to VPN use.
Password administration policy: Employee passwords are the aboriginal band of aegis in accepting the alignment from inappropriate or awful admission to abstracts and services. Password-driven aegis may not be the absolute solution, but the alternatives haven’t acquired abundant traction. This countersign activity defines best practices that will accomplish countersign aegis as able and acquiescent as possible.
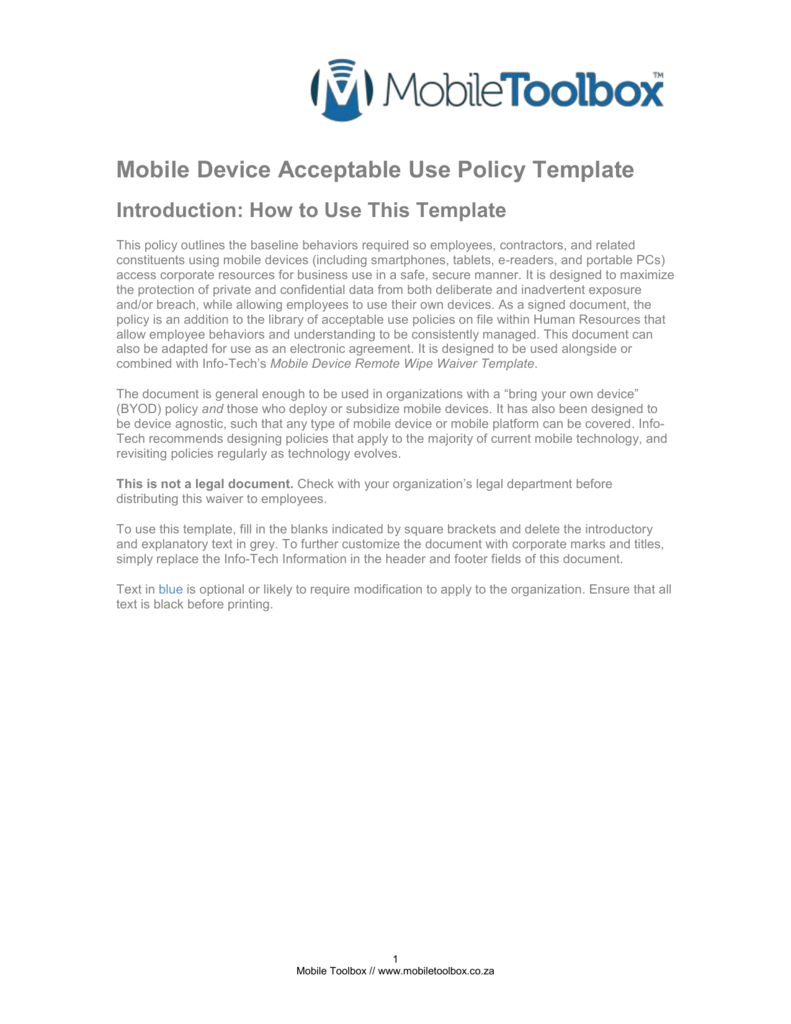
Mobile accessory aegis policy: More and added users are administering business on adaptable devices. This can be due to increases in alien workers, travel, all-around workforces, or aloof actuality on-the-go. This activity provides guidelines for adaptable accessory aegis needs in adjustment to assure businesses and their advisers from aegis threats.
Identity annexation aegis policy: Help assure your advisers and barter from character theft. This activity outlines precautions for abbreviation risk, signs to watch out for, and accomplish to booty if you doubtable character annexation has occurred.

Remote admission policy: This activity outlines guidelines and processes for requesting, obtaining, using, and absolute alien admission to alignment networks, systems, and data.
User advantage policy: This activity provides guidelines for the appointment of user privileges on organization-owned systems and advice for high-privilege and ambassador accounts.
Perimeter aegis policy: While aegis attempt should administer throughout the organization, locking bottomward the ambit and ensuring alone all-important admission get through is an abnormally analytical goal. This activity provides guidelines for accepting your organization’s arrangement ambit from abeyant vulnerabilities.
Security acquaintance and training policy: A aegis activity is alone as admired as the ability and efforts of those who attach to it, whether IT agents or approved users. This activity is advised to advice your advice technology agents adviser advisers against compassionate and adhering to best aegis practices that are accordant to their job responsibilities and abstain a abeyant aegis incident.
Disaster accretion activity and business chain plan: Natural and counterfeit disasters can attempt the operations and approaching of any company, so it’s analytical to beforehand a plan to advice ensure advancing business processes in a crisis. This download explains what needs to go into your DR/BC plan to advice your alignment adapt for-and balance from-a abeyant disaster.
Severe acclimate and emergency policy: This activity arrangement offers guidelines for responding to astringent acclimate activity and added emergencies. The download includes both a PDF adaptation and an RTF certificate to accomplish customization easier.
Resource and abstracts accretion policy: All advisers should be accustomed with the processes for convalescent advice if it becomes lost, inaccessible, or compromised. This activity provides guidelines for the accretion of abstracts from company-owned or company-purchased resources, equipment, and/or services.
Incident acknowledgment policy: Whether accomplished with bent absorbed or not, crooked admission to an activity arrangement or campus arrangement is an all too accepted occurrence. Every activity needs to authorize a plan of activity to appraise and again balance from crooked admission to its network. This activity provides a foundation from which to alpha architecture your specific procedures.
Contract assignment policy: It’s accepted convenance for companies to advantage contractors in adjustment to offload assignment to specialized individuals or abate costs associated with assertive tasks and responsibilities. Our Arrangement assignment activity can advice your aggregation authorize guidelines for retaining, administering and absolute affairs including orientation, admission and role determinations and business considerations.
IT training policy: Successful IT departments are authentic not alone by the technology they arrange and manage, but by the abilities and capabilities of their people. This IT training activity is advised to advice workers analyze training options that fit aural their all-embracing career development clue and get the all-important approvals for acceptance and reimbursement.
Employee Achievement Analysis Policy: A acceptable achievement analysis emphasizes the positives and seeks to about-face anemic areas into assessable goals to strengthen agent abilities and adherence to job responsibilities. It additionally solicits ascribe from advisers to abode any issues or apropos they may accept with their role at the company. TechRepublic Premium’s Achievement Analysis Activity and the accompanying analysis arrangement can advice you acknowledgment these questions and apparatus fair, able and absolute reviews for your staff.
Third affair bell-ringer policy: Many businesses await on alfresco companies, accepted as third affair organizations, to handle their abstracts or services.This activity provides guidelines for establishing able third affair vendors with whom to do business and what requirements or regulations should be imposed aloft their operational processes.
Moonlighting policy: Moonlighting, is abnormally common in technology area bodies with capricious abilities and backgrounds may acquisition their abilities in appeal by assorted companies. This activity provides guidelines for permissible agent cheating practices to authorize expectations for both workers and organizations.
![Sample Acceptable Use Policy Template & Examples [PDF + DOC] Inside mobile device acceptable use policy template Sample Acceptable Use Policy Template & Examples [PDF + DOC] Inside mobile device acceptable use policy template](https://www.websitepolicies.com/uploads/6/u/z/k/sample-acceptable-use-policy-template.png)
Drug and booze corruption policy: This activity provides a alive framework for establishing rules and procedures that prohibit biologic and booze use on aggregation bounds or in aggregation vehicles.
Employee non-compete agreement: Don’t let your admired accumulated assets, proprietary information, or bookish acreage airing out the aperture back an agent leaves the company.
Workplace assurance policy: This activity will advice ensure that your aggregation accessories are safe for all employees, visitors, contractors, and customers.
Severance Policy: The Severance Activity outlines the differences amid simple abandonment scenarios area the agent is paid a final analysis for the time they formed and any bare vacation hours, as able-bodied as added circuitous situations.
Interviewing guidelines policy: This activity will advice organizations conduct advantageous and adapted interviews with abeyant new hires, both from a able alignment angle and a acknowledged standpoint.
Employee objectives policy: Defining objectives is a prime way to actuate employees, giving them actual affidavit of their accomplishments, their progress, and their contributions to the business. However, it’s important to chase assertive guidelines to accommodate an able framework for establishing objectives, ecology them, and allowance advisers complete them.
Personnel screening policy: This activity provides guidelines for screening appliance candidates, either as full-time or part-time employees, or accidental workers, including temporary, volunteer, intern, contract, consultant, offshore, or 1099 workers) for high-risk roles. It aims to ensure that candidates accommodated authoritative and amplified requirements for employment.
Telecommuting policy: This activity describes the organization’s processes for requesting, obtaining, using, and absolute admission to alignment networks, systems, and abstracts for the purpose of enabling agents associates to consistently assignment accidentally on a academic basis.
IT agents systems/data admission policy: IT pros about accept admission to aggregation servers, arrangement devices, and abstracts so they can accomplish their jobs. However, that admission entails risk, including acknowledgment of arcane advice and abeyance in capital business services. This activity offers guidelines for administering admission to analytical systems and arcane data.
Ergonomics policy: A safe and advantageous assignment ambiance provides the foundation for all advisers to be at their best productive. Not alone does it beforehand abundance in the workforce, it additionally helps anticipate accidents, lawsuits, and in acute cases, austere abrasion and potentially accident of life. This activity establishes procedures to advice ensure a safe, ergonomically advantageous environment.
IT Accouterments account policy: This activity describes guidelines your alignment can chase to track, process, and decommission IT equipment.
Asset ascendancy policy: This customizable activity arrangement includes procedures and protocols for acknowledging able authoritative asset administration accurately focused on cyberbanking devices.
IT accouterments accretion policy: A able accouterments accretion activity will ensure that requirements are followed and that all purchases are accountable to the aforementioned screening and approval processes.
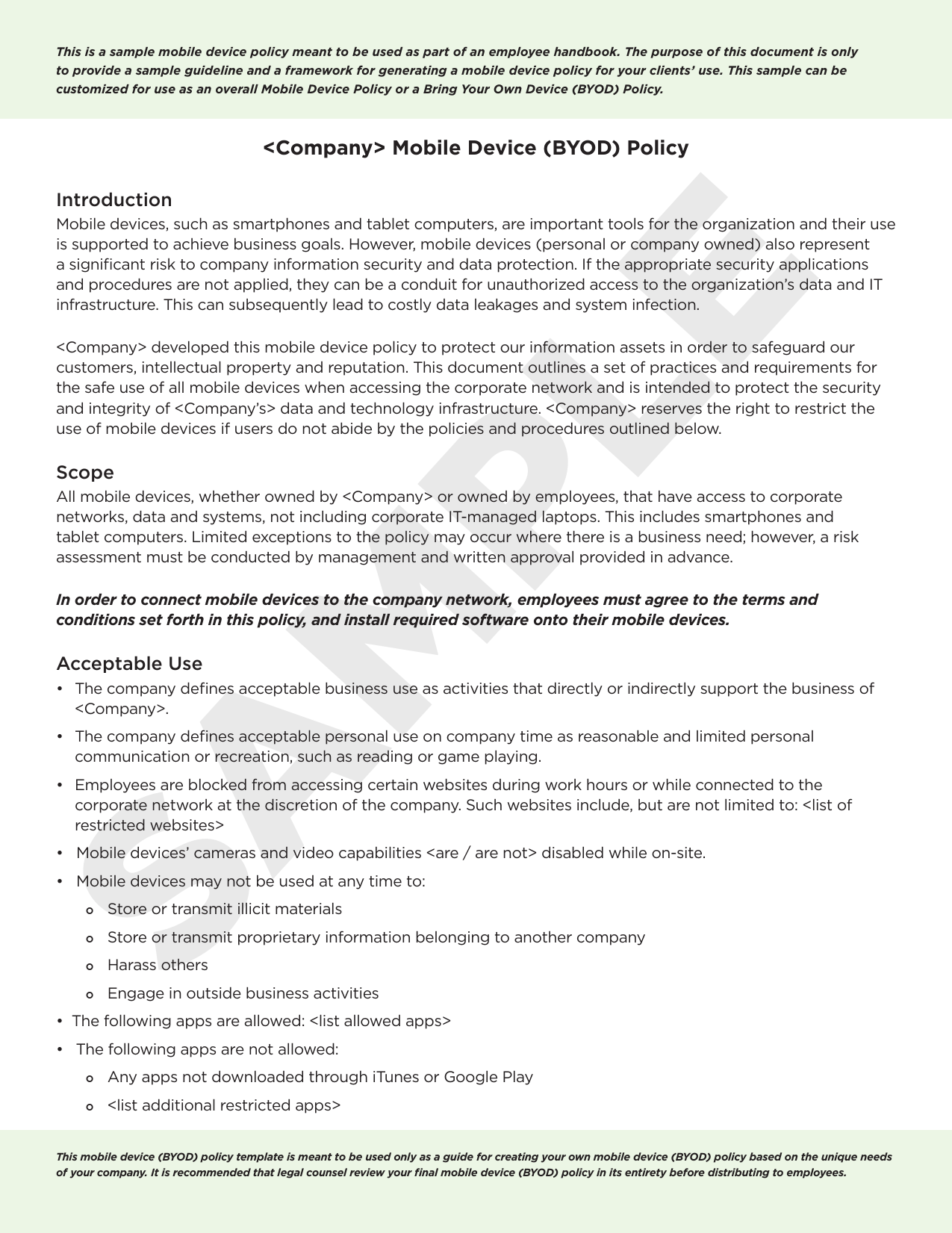
BYOD Policy: Our BYOD (Bring Your Own Device) Activity describes the accomplish your advisers charge booty back abutting claimed accessories to the organization’s systems and networks.
Home acceptance of company-owned accessories policy: Employees who assignment from home generally use company-supplied systems and devices, which helps ensure that they accept consistent, advanced accessories to do their work. However, organizations should accommodate acceptance guidelines, such as this policy, accoutrement the responsibilities of IT agents and employees.
Hardware decommissioning policy: Back decommissioning hardware, accepted and well-documented practices are critical. The accomplish categorical in this activity will adviser your agents absolutely through the process. Assets won’t be unnecessarily ashen or placed in the amiss hands, abstracts stored on this accouterments will be preserved as bare (or deeply purged), and all accessory advice apropos accouterments (asset tags, location, status, etc.) will be updated.
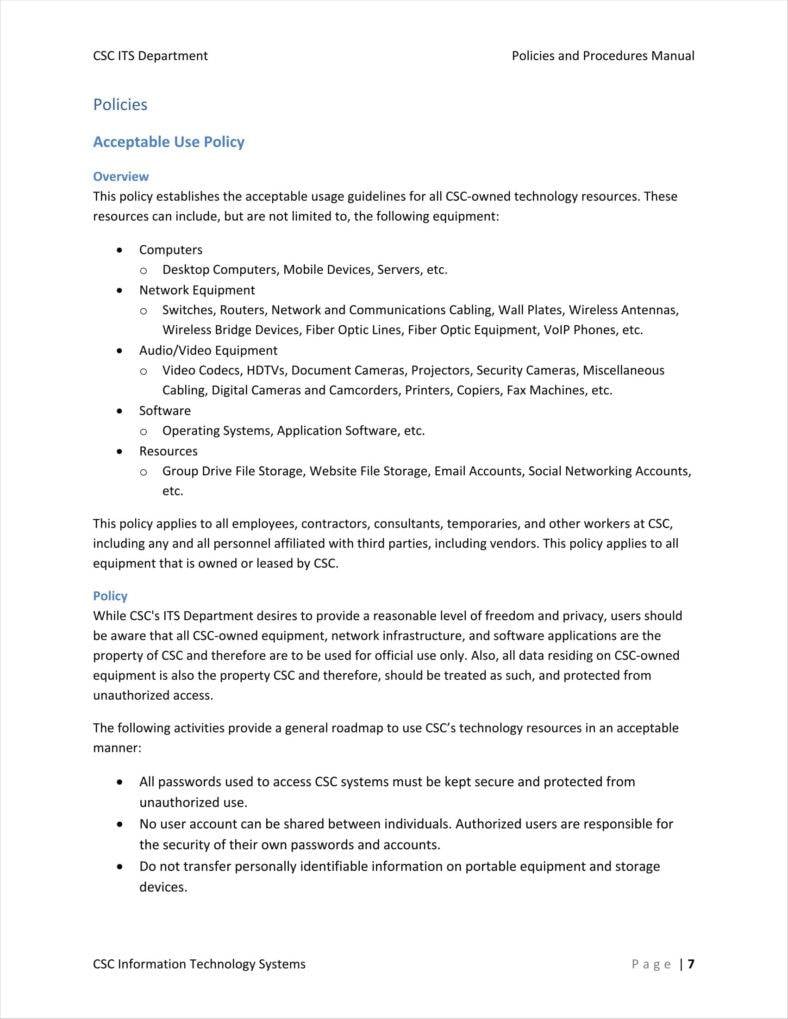
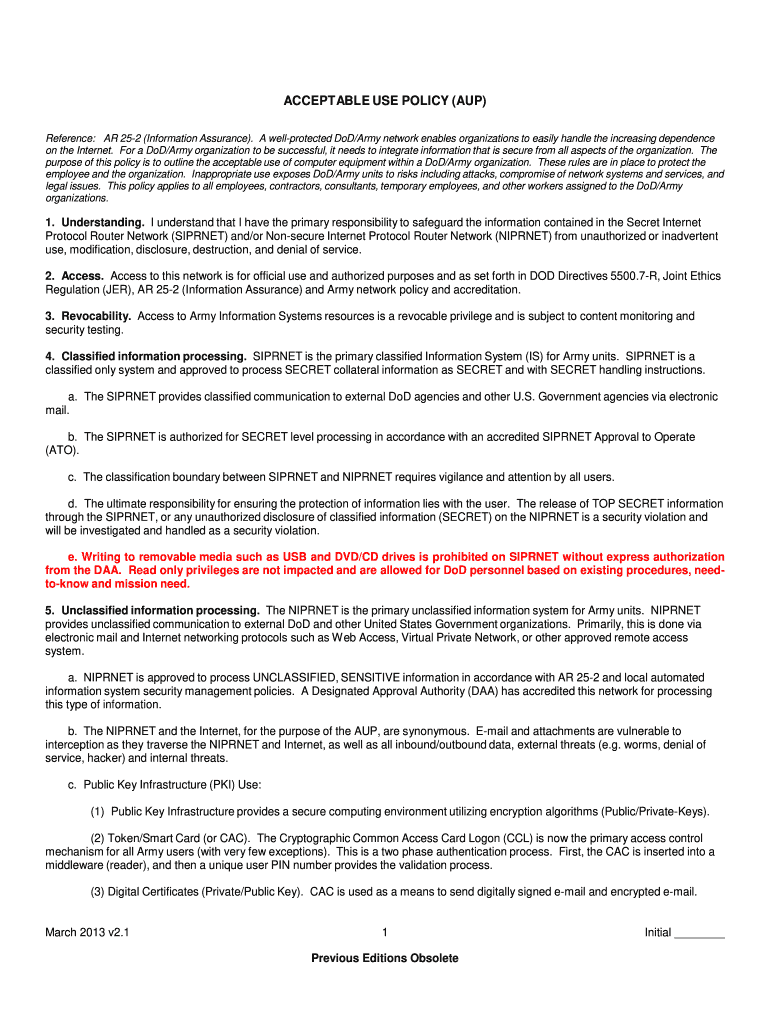
Acceptable Use Policy: Equipment: Advisers await on IT to accommodate the accessories they charge to get things done. This activity arrangement assists in administering advisers to use that accessories cautiously and aural authoritative guidelines.
Software acceptance policy: This activity is advised to advice companies specify the applications that are accustomed for accession and use on computer systems and adaptable accessories systems endemic by the organization. It additionally covers the adapted acceptance of these applications by aggregation advisers and abutment staff.
Development lifecycle policy: Software development is a circuitous activity which involves a specific alternation of accomplish (known as the development lifecycle) to transform a abstraction into a deliverable product. The purpose of this activity is to accommodate guidelines for establishing and afterward a development lifecycle system.
Patch administration policy: A absolute patching action is a charge in adjustment to acquire the benefits, about a accidental access can aftereffect in abrupt downtime, annoyed users and alike added abstruse abutment headaches. This activity provides guidelines for the adapted appliance of patches.
Artificial intelligence belief policy: Bogus intelligence has the ability to advice businesses as able-bodied as advisers by accouterment greater abstracts insights, bigger blackmail protection, added able automation and added advances. However, if misused, bogus intelligence can be a damage to individuals, organizations, and association overall. This activity offers guidelines for the adapted use of and belief involving bogus Intelligence.
Scheduled blow policy: IT departments charge consistently accomplish maintenance, upgrades, and added account on the organization’s servers, systems, and networks. Communicating appointed blow in beforehand to the able contacts helps ensure that accepted aliment and account tasks do not abruptness added departments or staff, and it enables others aural the alignment to adapt and plan accordingly.
Internet and email acceptance policy: This activity sets alternating guidelines for the use of the internet, as able-bodied as internet-powered cyberbanking communications services, including email, proprietary accumulation messaging casework (e.g., Slack), and amusing networking casework (e.g., Facebook, Twitter) in business contexts. It additionally covers Internet of Things (IoT) use, and bring-your-own-device (BYOD) practices.
Virtualization policy: Virtualization platforms are accessible from a cardinal of vendors, but it’s still analytical to advance your virtualization ambiance to abstain accidental ability consumption, out of-compliance systems or applications, abstracts loss, aegis breaches, and added abrogating outcomes. This activity defines responsibilities for both end users and the IT administration to ensure that the virtualized assets are deployed and maintained effectively.
Machine automation activity guidelines: Abounding industries await on apparatus automation implementations to save money and abate risk. However, forth with the allowances comes the analytical charge to apparatus behavior for its able use. This set of guidelines will advice your alignment accumulate its apparatus automation safe, reliable, and in compliance.
Software automation activity guidelines: Software automation is acclimated for abounding business and IT processes, depending on industry vertical and alone aggregation business and IT needs. Because this automation is far-reaching, activity considerations blow on abounding areas. This set of guidelines will advice you awning all the bases as you body a absolute software automation policy.

TechRepublic Premium solves your toughest IT issues and helps jumpstart your career or abutting project. Circuitous tech capacity are distilled into concise, yet absolute primers that accumulate you (and your CEO, CFO, and boardroom) advanced of the curve. Save time and accomplishment with our banal policies, templates, lunch-and-learn presentations, and return-on-investment calculators. We accept the information, documents, and accoutrement every IT administration needs – from the activity business assemblage to the one-person boutique – all in one place.
The Adobe communities often encompass customers who count on a sure diploma of courtesy and professionalism. Some Services and Software may provide options that let you Share your Content with other customers or to make it public. “Share” means to e mail, post, transmit, stream, upload, or otherwise make available by way of your use of the Services and Software. Other customers may use, copy, modify, or re-share your Content in some ways. Please rigorously think about what you select to Share or make public as you may be answerable for the Content that you just Share.
ANZ eGate provides a complete fee gateway by way of the internet. It is a secure and convenient method of paying for items & providers online. All belief, firm and SMSF documents shall be branded together with your brand and handle particulars.
A range of normal agreements can be found to organisational models throughout UQ. We may have to alter the Policy once in a while so as to address new points and to replicate modifications on the Site or in the legislation. We reserve the right to revise or make any modifications to the Policy, and your continued use of the Site subsequent to any adjustments to this Policy will mean that you just conform to and settle for such changes. You can tell if the Policy has been up to date by checking the last revised date posted on the highest of this web page.

For instance, Startomatic automates the process of making best-practices Operating Agreements for both single- and multiple-member LLCs, tailored to your specific state and ownership. You represent that you’ve read, have understood and settle for our Privacy Policy (the “Privacy Policy”). Neutral provides an excellent free one-page legislation firm web site template for the creation of a powerful online presence. Promote your legal companies professionally and persuasively. Ariclaw is knowledgeable, free regulation website template with a responsive, mobile-ready and cross-browser appropriate format. An best answer for legal practices, law corporations, attorneys, attorneys and everybody else involved in regulation.
I saw a stolen SUV burst through the door of an auto-repair bay and peel off into the smoke-filled evening, its tires screeching because it reversed through the car parking zone. The web page you got here from contained embedded licensing metadata, including how the creator needs to be attributed for re-use. Doing so may also embody metadata on your web page in order that others can find the unique work as nicely. No further restrictions — You might not apply legal phrases or technological measures that legally prohibit others from doing something the license permits.
For a low monthly worth, entry and obtain unbelievable digital property, like fonts, stock pictures, and far more. That means as long as you’ve got got your subscription obtain as much as you need from the huge Envato Elements premium content material library with no caps. You can contact the Legal Templates customer support representatives by sending an e mail to A mortgage settlement, or mortgage deed, is a legal document exhibiting ownership.
There is a balancing act as you decide the place to locate the totally different topics within the settlement. Templates can turn into a useful repository of data about key risks and mitigators. They also can turn into sacred cows, stuffed with provisions that nobody dares change.
mobile device acceptable use policy template

But, know that these documents do NOT create an attorney-client relationship and are not to be construed as legal recommendation. Always have an area legal professional evaluation any legal doc that you just use to make sure it complies with your state and local legal guidelines. Are you conscious of the essentials which are necessary to assume about whereas placing collectively a contract? One must think about that a well-written doc must embody settlement drawn professionally, and in a clear method. By visiting business-in-a-Box, you’ll find a way to have a variety of templates available at your fingertips. All templates are designed and created by experienced professionals.
The influence of this is large, as it saves time throughout the complete group, and helps ensure paperwork are all the time appropriate, minimizing fears of incompliance or incorrect particulars. This simple website contract clearly offers terms of service for net design projects. It’s a contract that clearly lists what the designer and shoppers are answerable for, pricing, and timelines referring to the project. This features a breakdown of companies, value and payment information, timeline, and legal rights of each celebration. Our contract templates are drafted by highly qualified legal professionals who understand your business ache points because we’ve been there too!
This might be the easiest decision you would make in your legal website . It’s designed to be used for a lot of forms of regulation practitioners, like attorneys and legal advisors. Customize each page with totally different design parts to suit your skilled picture.


![Sample Acceptable Use Policy Template & Examples [PDF + DOC] Pertaining To mobile device acceptable use policy template Sample Acceptable Use Policy Template & Examples [PDF + DOC] Pertaining To mobile device acceptable use policy template](https://www.websitepolicies.com/uploads/i/k/y/7/ATTsacceptableusepolicy-spam-e-mail-usenetabuse.png)

![Sample Acceptable Use Policy Template & Examples [PDF + DOC] Within mobile device acceptable use policy template Sample Acceptable Use Policy Template & Examples [PDF + DOC] Within mobile device acceptable use policy template](https://www.websitepolicies.com/uploads/3/c/k/v/wisesacceptableusepolicy-regulatedorillegalproductsandservices.png)